Stryker Cyberattack 2026: Timeline, Impact, and Cybersecurity Lessons for Global Healthcare
In March 2026, global medical technology leader Stryker Corporation suffered a significant cybersecurity incident that impacted corporate systems globally. Stryker confirmed the incident affected parts of its internal network, while attackers separately claimed thousands of devices were wiped. Those attacker claims have not been independently verified.
Some security analysts have speculated that the intrusion may have been politically motivated, based on the group that claimed responsibility and the nature of the tools used. No official attribution has been confirmed at this time.
In this article, we review the timeline of the Stryker cyberattack, the threat actor that claimed responsibility, the operational impacts, and key cybersecurity lessons for organizations globally.
About Stryker Corporation
Stryker Corporation is one of the largest medical technology companies in the world, producing surgical equipment, orthopedic implants, and medical devices used in hospitals globally.
Founded in 1941 and headquartered in Michigan, the company supports healthcare systems across more than 100 countries. Because of its role in the medical supply chain, any disruption to its operations can potentially affect healthcare providers worldwide.
Timeline of the Stryker Cyberattack
Rising Cyber Tensions (Early March 2026)
Before the attack occurred, the broader threat landscape was already showing signs of increased hacktivist activity. Security agencies including CISA have previously warned that politically motivated threat actors are increasingly targeting critical infrastructure sectors, including healthcare.
Hacktivist groups aligned with geopolitical causes have used cyberattacks as a tool of disruption against Western organizations, a trend documented across multiple government and industry threat reports.
Initial Network Disruption (March 11, 2026)
On March 11, 2026, employees across many regions started experiencing sudden outages to several internal corporate systems.
Key issues reported included:
- Employees unable to log into company systems
- Corporate devices becoming locked or wiped
- Internal communication platforms failing
Wiper Malware Deployment
Security researchers believe the attack used wiper malware because it does not function like standard ransomware attacks which demand ransom payments. Wiper malware is designed to permanently destroy data rather than encrypt it for financial gain.
Note: The following figures come entirely from the attacker group's own statements and have not been independently verified. Threat actors routinely exaggerate claims to maximize public impact.
With that context, the group alleged:
- Over 200,000 devices wiped (attacker claim, unverified)
- Approximately 50 terabytes of data stolen (attacker claim, unverified)
Some reporting has suggested a possible link to Iranian-affiliated threat actors, though no government body has officially confirmed this attribution as of the time of writing.
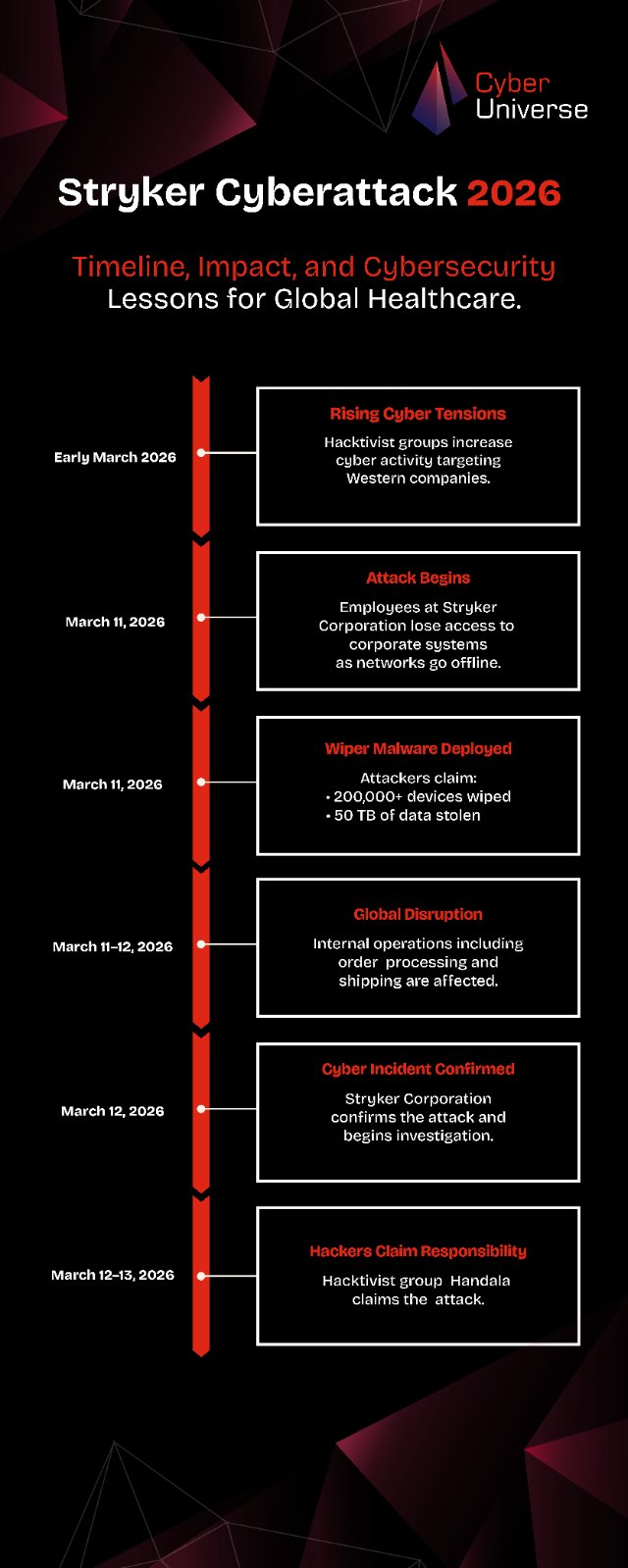
Global Operational Disruption
The cyberattack quickly impacted several internal business processes. Reports suggested disruptions in:
- Order processing systems
- Manufacturing coordination
- Global shipping and logistics (Reuters)
However, the company confirmed that medical devices used in hospitals were not affected, due to network separation between clinical systems and corporate infrastructure.
Public Disclosure and Investigation
Following the incident, Stryker Corporation confirmed it was investigating a cybersecurity event affecting parts of its internal network. The company stated it had engaged external cybersecurity experts and incident response specialists to investigate the breach. Stryker also indicated it was cooperating with relevant government authorities, though the specific agencies involved were not named in public statements at the time of writing.
Hacktivist Group Claims Responsibility
A hacktivist group known as Handala claimed responsibility for the attack through posts on social media. Handala is a pro-Palestinian hacktivist group that has previously claimed cyberattacks against Israeli and Western targets, often framing its operations as acts of political retaliation. The group stated the Stryker attack was linked to ongoing geopolitical conflicts, though this motive has not been independently confirmed by investigators or government authorities.
Cyber attribution is inherently difficult. Hacktivist groups can falsely claim attacks for visibility, and independent verification from a government body or named threat intelligence firm has not been publicly released at this time.
Cybersecurity Lessons from the Stryker Attack
The incident highlights several key lessons for organizations, particularly in healthcare and medical technology.
Healthcare Infrastructure Is a Growing Cyber Target
Healthcare companies hold sensitive data and operate critical infrastructure, making them attractive targets for cybercriminals and politically motivated hackers.
Wiper Attacks Are Increasing
Unlike ransomware, which seeks financial payment, wiper malware is designed purely for destruction, permanently deleting or overwriting data with no recovery mechanism. The use of wiper malware has grown significantly in recent years, particularly in conflict zones. Microsoft's Security Response Center and ESET Research have both published detailed findings on this trend.
Identity Systems Are High Value Targets
While the specific attack vector in this incident has not been publicly confirmed, the scale of the disruption is consistent with attacks that compromise endpoint or device management platforms. When these systems are breached, attackers can push destructive commands across thousands of managed devices at once.
Network Segmentation Protects Critical Systems
One important takeaway from the incident is that medical devices remained operational, thanks to network segmentation separating clinical systems from corporate networks. This highlights the importance of strong cybersecurity architecture in healthcare environments.
Conclusion
The 2026 cyberattack on Stryker Corporation demonstrates how cyber threats are evolving beyond financial crime and into the realm of geopolitical disruption.
As healthcare systems become increasingly digital, organizations must invest in stronger cybersecurity frameworks to protect critical infrastructure.
For hospitals, manufacturers, and technology providers, the incident is a reminder that operational disruption in the medical supply chain carries real downstream risk. While patient care was not directly affected in this case, attacks on healthcare manufacturers can delay device supply, interrupt logistics, and ultimately affect care delivery if resilience measures are not in place.
Sources
- Stryker Corporation, Official Customer Message, March 2026
- Reuters: Stryker Flags Disruption to Orders and Manufacturing, March 12, 2026
- Tom's Hardware: Iran Hacking Group Claims Attack on Stryker
- Economic Times: What Is Wiper Malware and Will Stryker Recover
- Economic Times: Iranian-linked Hackers and Wiper Malware
- Microsoft Security Blog: Destructive Malware Targeting Ukrainian Organizations
- ESET Research: New Wiper Malware Used in Ukraine
- CISA: Cyber Threats and Advisories
FAQ
What happened in the Stryker cyberattack in 2026?
The 2026 cyberattack on Stryker Corporation disrupted the company’s internal global network and disabled thousands of employee devices. The attack reportedly involved destructive malware that wiped systems instead of demanding ransom. It temporarily affected corporate operations such as order processing, logistics, and manufacturing coordination.
Who was responsible for the Stryker cyberattack?
A hacktivist group called Handala claimed responsibility for the attack. The group suggested the cyberattack was politically motivated and linked to geopolitical tensions. However, official attribution in cyber incidents typically requires extended investigation by cybersecurity experts and government agencies.
Was patient data or medical equipment affected in the Stryker cyberattack?
According to company statements, medical devices used in hospitals were not impacted by the attack. Corporate IT systems experienced disruption, but clinical equipment and patient-connected technologies were protected through network segmentation.
What type of malware was used in the Stryker cyberattack?
Security researchers believe the attack involved wiper malware, which is designed to permanently destroy data and disable systems. Unlike ransomware, wiper attacks focus on disruption and sabotage rather than financial gain.
How many systems were affected in the Stryker cyberattack?
Hackers claimed that more than 200,000 devices were wiped and approximately 50 terabytes of data were stolen during the attack. While these numbers have circulated in reports, the exact scale of the impact has not been fully confirmed publicly.
Why are healthcare companies targeted by cyberattacks?
Healthcare organizations are attractive targets because they store sensitive patient information and operate critical infrastructure. Medical technology companies like Stryker Corporation are also part of the global healthcare supply chain, making them high-value targets for cybercriminals and politically motivated attackers.
What cybersecurity lessons can companies learn from the Stryker attack?
The Stryker incident highlights several important cybersecurity practices, including strong network segmentation, identity protection, endpoint security, and proactive incident response planning. Organizations must also prepare for destructive cyberattacks that aim to disrupt operations rather than demand ransom.




